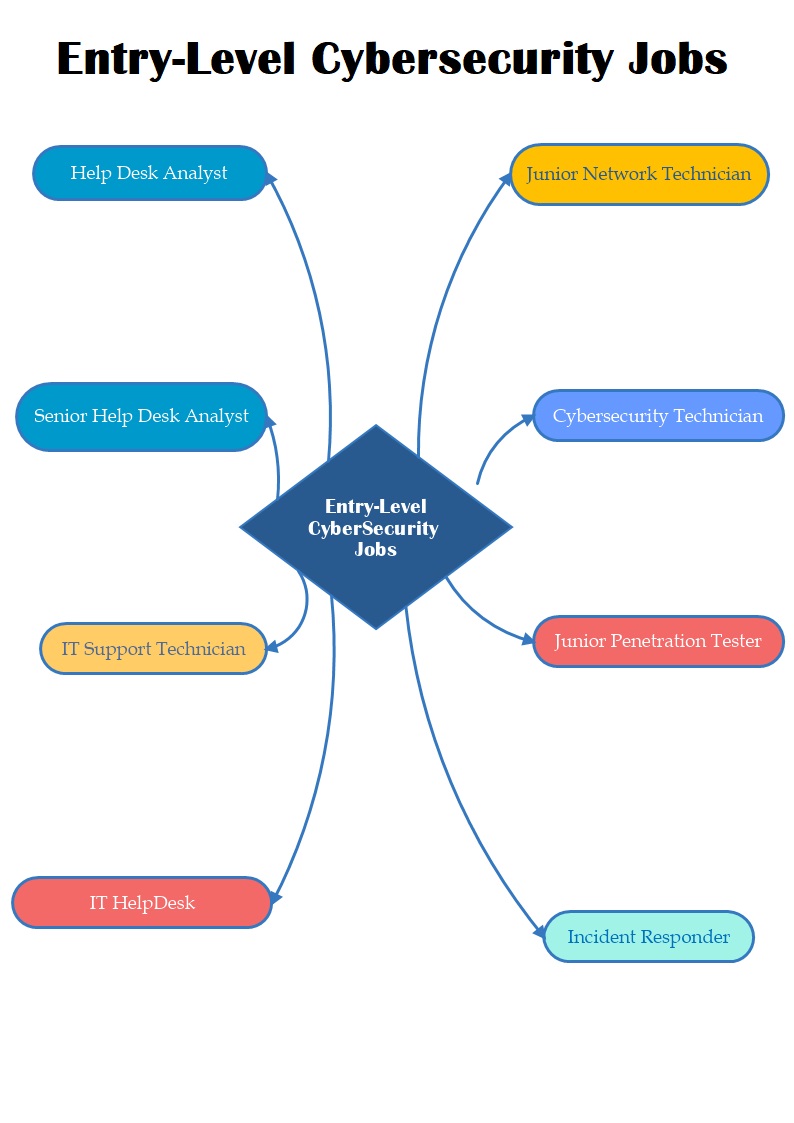
There is a wide range of cybersecurity career paths, from network administrators to software engineering and many more as this list of cybersecurity job titles will demonstrate:
Information Security Officer
An information security officer is a security manager who is responsible for implementing and managing the information security policies, practices, security measures, and procedures within an organization. These security managers work with IT specialists to develop, maintain, and implement the policies, procedures, and technologies that protect the organization’s information assets. They ensure that information security is included in all of the organization’s business processes and technology systems. They also ensure that assets are adequately protected from physical security threats, such as fire and theft; and from cyber threats, such as intentional or unintentional disclosure of confidential information.
Security Consultant / Security Specialist
A Security Consultant is someone who is employed by a company or organization, typically in the IT industry, to offer advice and assistance in areas such as network security and data protection. They will take
Cybersecurity Analyst
A Cybersecurity Analyst is someone who works to protect information assets by identifying, measuring, and mitigating security risks. Cyber security analysts are often responsible for developing cybersecurity strategies and managing IT infrastructure.
A Cybersecurity Analyst works in the IT industry and is responsible for managing data protection and network security. They also work to identify risks, threats, and vulnerabilities through research. A Cybersecurity Analyst will typically work with IT policies to set up a framework that enables the security of information and network resources.
Cloud Security Architect
A Cloud Security Architect is a person who is qualified to design and implement security measures in an organization’s cloud environment. This person’s job is to ensure data security, access levels, and necessary maintenance of the cloud infrastructure. A Cloud Security Architect will engage with stakeholders from both the IT and business sides of an organization.
Ethical Hacker / Penetration Tester
Ethical hackers are individuals that have a strong passion for security and ethical hacking, and they dedicate themselves to finding vulnerabilities in computer systems.
They use the same tools as criminal hackers, but their goal is to find vulnerabilities in a system before the bad guys do. They are often the first line of defense against cyber threats. A Cloud Security Architect will work with ethical hackers to make sure that their testing does not break production systems.
Chief Information Security Officer
Chief Information Security Officers (CISOs) are the head of a company’s IT security department. They are responsible for overseeing their organization’s security policies, planning and implementing security measures to combat cyber threats, managing and improving security systems, and ensuring that the company is in compliance with government and industry regulations. CISOs are also responsible for managing relationships with external companies in their industry to ensure they are implementing best practices.
Cybersecurity Auditor
Security auditors may work for a government agency that investigates and evaluates the effectiveness of an organization’s information security program. This includes the organization’s information systems, information-technology network, and information security personnel. The results of an audit are used to monitor the level of protection against system vulnerabilities, evaluate compliance with security policies, and detect fraud and negligence related to information security.
The goal of cyber security auditors is to provide evidence that the organization’s information security program is effectively implemented and operating according to policy. Audits are performed by independent, experienced cyber security auditors.
Network Security Engineers
Network Security Engineers are capable of managing network security at both the organizational and individual levels. They are in charge of detecting and preventing cybersecurity risks such as malware.
Security Software Developers
Security software developers are people who develop software that can be used for different security purposes. They can design and develop security programs or systems for organizations to use. Security software developers are in charge of creating software that is used to secure computer networks, individual computers, websites, mobile devices, etc.
Cybersecurity Engineers
Cybersecurity engineers are IT professionals who specialize in computer security. They focus on the design and implementation of software or hardware systems to maintain the integrity and confidentiality of data.
So, Cybersecurity engineers are the ones who have to ensure that the data is protected from unauthorized access. What do Cybersecurity Engineers do? Cybersecurity engineers are responsible for designing and implementing software or hardware systems to ensure the integrity and confidentiality of data.